Introduction
It’s been three and a half years since I wrote the first ASM product update. While we’ve posted updates every month since, this is only my second.
Looking back at that first post feels a bit surreal. The product was simpler, the scope smaller (our logo was even red). We had just released the scan overview page. No reports, no notifications. Since then, a lot has changed. We’ve helped build a National Picture of Risk for Jisc across the .ac.uk estate two years in a row, introduced actions to group and prioritise risks, and expanded our detections and discovery to give far deeper visibility into the attack surface.
It’s been a steady build, month by month—but it’s only when I look back at that first blog that I can really see what we’ve built at Hexiosec, and feel proud of it.
Now, let’s look at what we delivered this month.
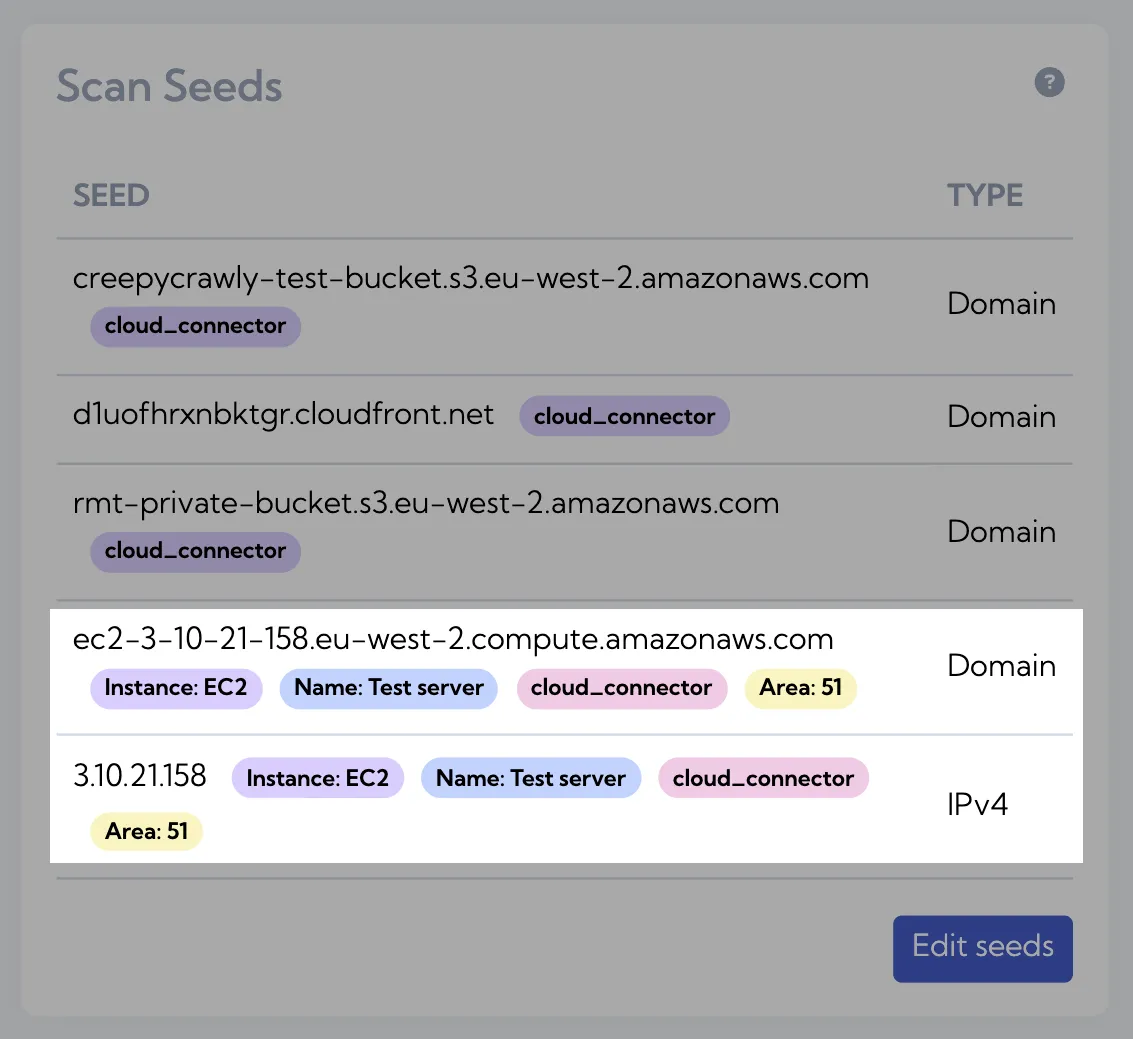
AWS resource tags now visible in ASM
When discovering assets via Cloud Connector, context is everything. This month, we’ve started extracting tags from AWS resources and surfacing them directly in ASM alongside the seeds we create.
View our Cloud Connector on GitHub
This means you don’t just see what was discovered, but how it’s described in your environment — whether that’s ownership, environment, or cost centre. It makes it easier to triage findings, understand intent, and route issues to the right place without needing to cross-reference in AWS.
Tags are currently visible on seeds, providing immediate context at the point of discovery.
We’re continuing to build on this in Q2, where we’ll expand tag functionality to support filtering and risk analysis based on tags.
security.txt checks now included in ASM
When assessing your external attack surface, clear disclosure matters. This month, we’ve added support for detecting and validating security.txt files.
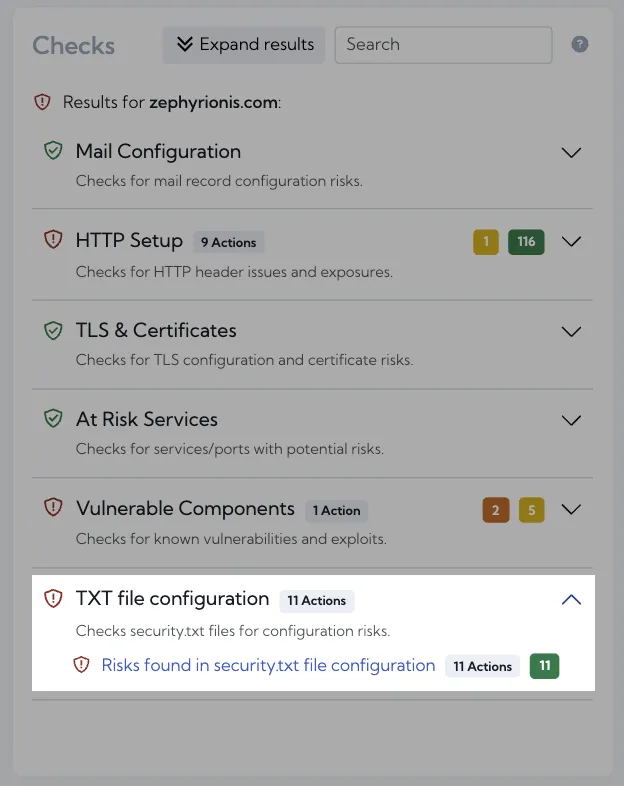
A security.txt file is a standard way to tell security researchers how to report vulnerabilities. Without it, responsible disclosure becomes harder, slower, or missed entirely.
We now check for the presence of a security.txt file in the expected locations and validate it against RFC 9116. This includes ensuring required fields like contact and expiry are present and correctly formatted, as well as identifying issues that may cause the file to be ignored.
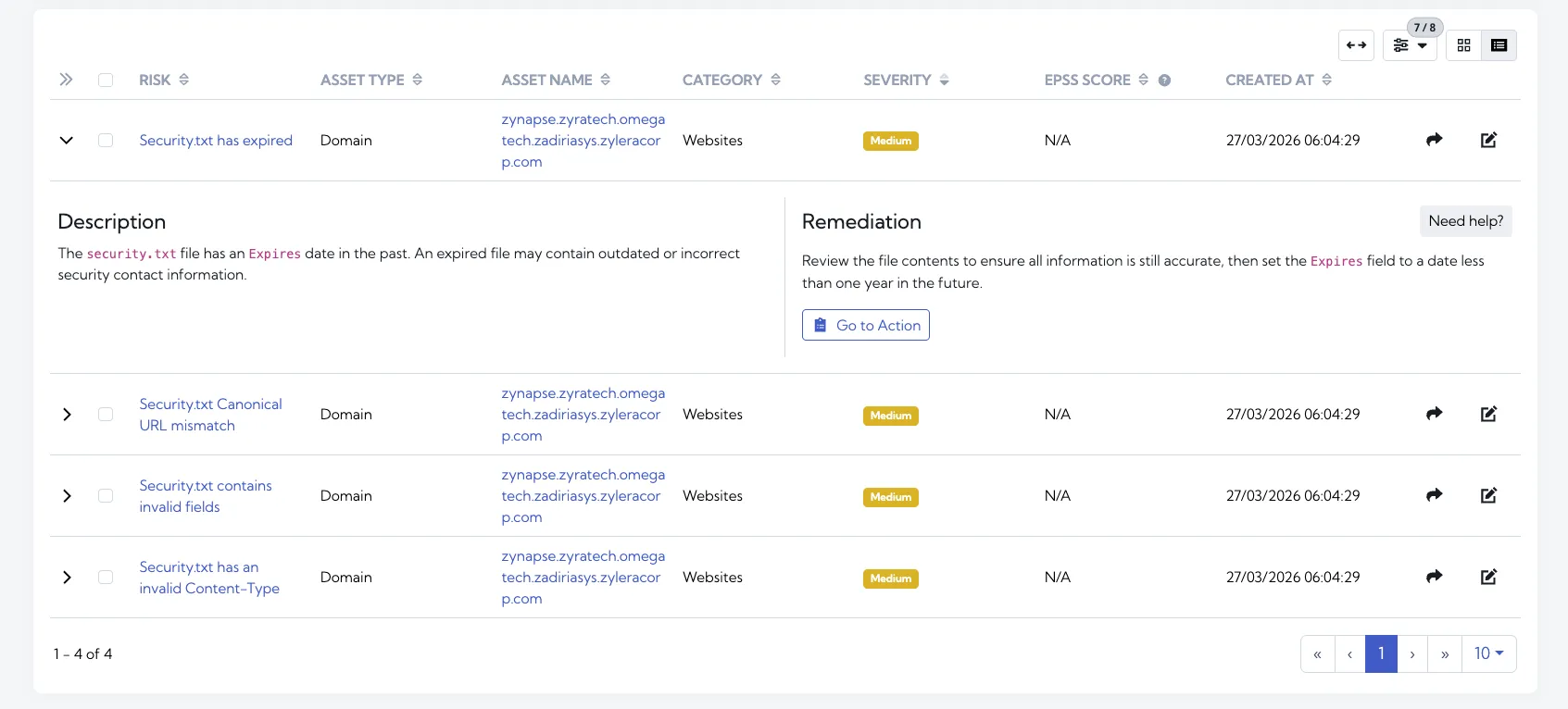
Where found, the file is surfaced directly in ASM, including its contents and a snapshot of how it appears externally. This gives you immediate visibility into how your disclosure policy is presented to the outside world.
Coming soon
We’re continuing to focus on improving how you prioritise and work through large volumes of data in ASM. Here’s what’s coming next:
-
Tags for results
When a scan produces a large number of results, it can be difficult to manage and prioritise them effectively. We’ll be introducing tagging, allowing you to organise results, filter more easily, and focus on what matters most.
-
More contextual risk descriptions
We’re enhancing risk descriptions to include more context about the specific asset they’re raised on. This will make it clearer why something matters and help you take action faster.
-
Improved performance for large scans
For larger scans, we’re working on improvements to how results are loaded. Initial data will be available sooner, with the rest continuing to load in the background to reduce waiting time.
-
robots.txt checks
Building on our work with domain policy files, we’ll be adding support for detecting and validating robots.txt, helping you ensure crawler directives are correctly configured and understood.
If there are other features you’d love to see in Hexiosec ASM, or Hexiosec Transfer (our true end-to-end encrypted file transfer app), please let us know.